Techno-Domination
Under neoliberalism, state and corporate power have fused to impose new forms of social control, using technology to transform private life into a system of total domination.
Mass Surveillance and “Smart Totalitarianism”
- Issue #4
- Author
Standing outside the Topography of Terror in Berlin, looking at its grey neutral exterior, it is hard to comprehend the magnitude of Nazi horrors that emanated from these grounds. Today’s hop-on, hop-off buses ferry tourists to and from the museum to visit Cold War graffitied remnants of the Berlin Wall, the nearby Checkpoint Charlie and the historic but modernized Bundestag building. On these grounds, however, stood institutions that were central to systems of Nazi persecution and terror.
From 1933 through 1945, before being destroyed and dismantled, buildings here housed the Secret State Police (Gestapo), the leadership of the SS (Protection Squad of the Nazi Party) and the Reich Security Main Office. These institutions used cold and brutal methods to serve cold and brutal purposes. Following World War II, Communist Party secret police in East Germany surveilled people’s mail, telephone calls and foreigners. With 500,000 professional and civilian informants — and estimates as high as 2 million (if occasional informants are included) — to monitor a population of 17 million, the Stasi have been described the most intrusive surveillance organizations in world history.
Totalitarian regimes in Germany made widespread use of mass surveillance in order to dominate freedom and carry out horrific crimes. It is no surprise then that Germany is today a top-ranking country globally for data privacy and protection laws, that Berlin has evolved to become one of the world capitals for hackers and data privacy advocates, and that one of the first peer-to-peer computational platforms to guarantee user privacy against unwanted electronic surveillance, Enigma, is named after the tool that the Nazis used to broadcast coded messages from. Yet, ironically, the power of today’s mass surveillance systems — like those of the NSA, brought to light by Edward Snowden’s revelations — far exceed what previous totalitarian regimes could have imagined. Surveillance has spread like a pandemic.
Snooping on Ordinary Citizens
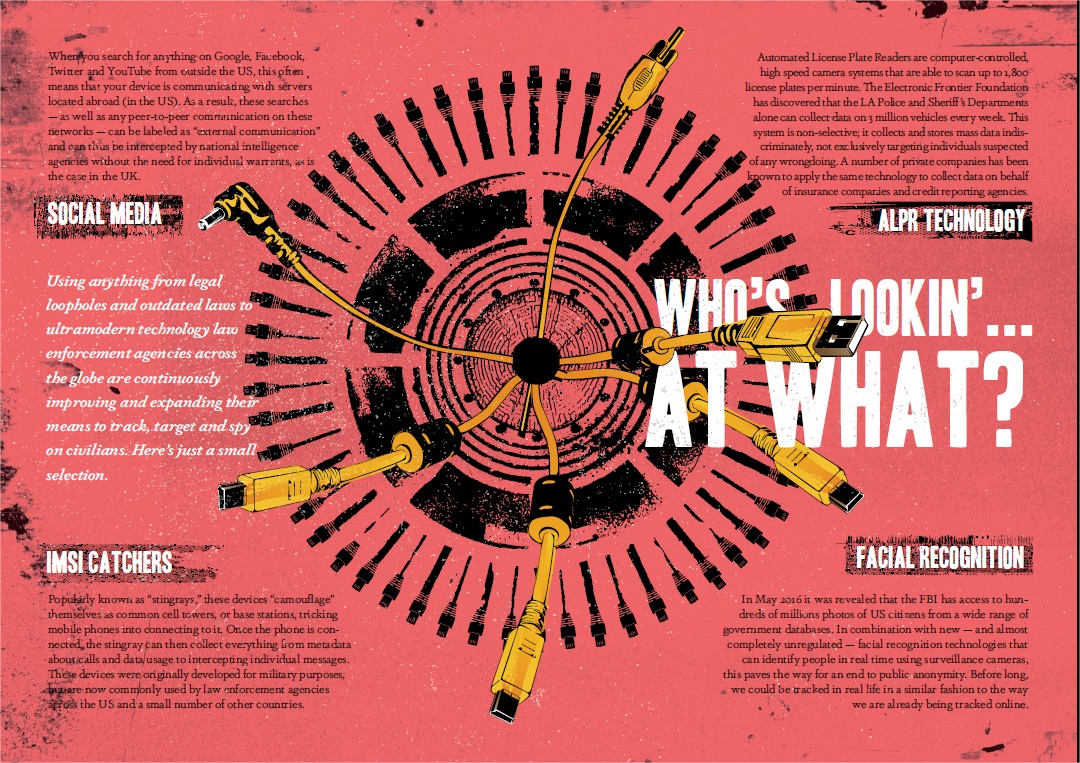
Mass surveillance, Privacy International explains, is the subjection of a population or significant component of a group to indiscriminate monitoring. “Any system that generates and collects data on individuals without attempting to limit the dataset to well-defined targeted individuals is a form of mass surveillance,” it writes.
 The NSA, above all, has deployed egregious techniques for mass surveillance and cyber warfare. Thanks to Snowden we now know about the secretive “Five Eyes” alliance, a multilateral surveillance arrangement between the United States, Canada, Australia and New Zealand that enables each participating state to spy on its own citizens by farming out the task to other participating states. More recently, in August 2016, an entity known as the “Shadow Brokers” leaked controversial NSA cyber weapons that a former NSA staff member described as the “keys to the kingdom.” Through malware infections and security exploits the NSA used these tools for years to hack individuals, companies and governments. The agency exploited vulnerabilities in widely used corporate security software systems, such as Cisco, without ever informing the company about their security problems.
The NSA, above all, has deployed egregious techniques for mass surveillance and cyber warfare. Thanks to Snowden we now know about the secretive “Five Eyes” alliance, a multilateral surveillance arrangement between the United States, Canada, Australia and New Zealand that enables each participating state to spy on its own citizens by farming out the task to other participating states. More recently, in August 2016, an entity known as the “Shadow Brokers” leaked controversial NSA cyber weapons that a former NSA staff member described as the “keys to the kingdom.” Through malware infections and security exploits the NSA used these tools for years to hack individuals, companies and governments. The agency exploited vulnerabilities in widely used corporate security software systems, such as Cisco, without ever informing the company about their security problems.
Widely used metaphors for understanding today’s mass surveillance — such as references to Nazi Germany, the Stasi or George Orwell’s Big Brother — run the risk of distracting attention from the horrors and crimes of past totalitarian regimes. But as measures against present abuses of power, like the fact that the NSA can collect 5 billion cell phone records per day, such comparisons can offer important insight. The Germany-based OpenDataCity compared the volume of records that the Stasi stored to the NSA’s capacity to store data. They determined that Stasi files would fill 48,000 filing cabinets, while just a single NSA server would fill 42 trillion filing cabinets. The organization concludes that the NSA can capture 1 billion times more data than the Stasi could.
Stasi files would fill 48,000 filing cabinets, while just a single NSA server would fill 42 trillion filing cabinets.
It is not just the NSA that snoops on ordinary citizens, however. In October 2016, the United Kingdom’s investigatory powers tribunal ruled that the country’s security services (GCHQ, MI5 and MI6) illegally collected huge quantities of communications data, “tracking individual phone and web use and other confidential personal information, without adequate safeguards or supervision for 17 years.” The security services no longer have to be concerned about the legality of their actions, however, because the very next month the Investigatory Powers Bill — also known as the “snooper’s charter” — was approved, thus legalizing mass digital surveillance in the country.
Controlling Critical Junctures
Today, governments and corporations control critical junctures of the web, including domain mapping, underwater cables, software and hardware, programming code, and data centers. This means that the web is now highly centralized, surveilled, studied, manipulated, and subject to damaging data breaches. Many are concerned that because of the emerging Internet of Things — including “smart homes”, “smart cities” and wearable technologies — there will soon be an explosion in collectable personal data, from your expired milk to your blood pressure, and more. This has opened doors to a plethora of ethical problems.
The collection and centralization of personal data has already enabled extraordinary social experiments. The US Department of Defense has studied extensively how to influence users on Facebook, Twitter, Pinterest and Kickstarter to understand social connections and how messages spread among networks. These messages included news relating to Occupy Wall Street and the “Arab Spring” uprisings. And separately, Facebook controversially sought to learn how to influence user emotions by manipulating its news feed.
The World Wide Web has entrenched systems of power by enabling them to strategically and surreptitiously influence networks and “nudge” populations in one direction or another. This is what Luciano Floridi, Professor of Philosophy and Ethics of Information, describes as the new “grey power.” Grey power is not ordinary socio-political power or military power, Floridi explains. It is not the power to directly influence others, but rather the power to influence those who influence power.
In the nineteenth and twentieth centuries, the industrialists in grey suits were the ones who held grey power, Floridi argues. Today, it is those controlling the social networks, the search engines and the industries around digital technology who hold grey power. The Google Transparency Project, for instance, has identified 258 instances of “revolving door” activity between Google and the US Federal Government, Congress and national political campaigns during President Obama’s eight-year term in office. These revolving doors move between White House officials, former national security, intelligence and Pentagon officials who left the administration to work for top positions in Google, and Google executives who joined top echelons of power in the White House and the Department of Defense.
The dangerous power of mass surveillance therefore does not reside only with the totalitarian regimes of the past. Modern forms of surveillance are used by companies and governments alike, sometimes working ubiquitously together to exploit, manipulate and influence the general population. No matter the motivations behind these invasive systems, it is clear that they are always dangerous, especially if they fall into the wrong hands.

The Wrong Hands
The threat of a far-right white supremacist movement rising to the surface in the US has long been a possibility. But few could have imagined that billionaire businessman Donald Trump would actually win the US presidential election. That possibility alone was hard to accept. He had no prior experience holding public office. But the sobering reality is starting to sink in. As US “commander-in-chief,” this dangerous man will have his hands on the levers of power overseen by the previous administration of Barack Obama. This includes the powers of mass surveillance and weapons of mass destruction.
Writing in Time Magazine the day after Trump’s upsetting victory, transgender and digital rights activist Evan Greer observed that Obama has “a matter of weeks to do one thing that could help prevent the United States from veering into fascism: declassifying and dismantling as much of the federal government’s unaccountable, secretive, mass surveillance state as he can — before Trump is the one running it.” On November 10, Edward Snowden tweeted: “The powers of one government are inherited by the next. Reforming them is now the greatest responsibility of this president, long overdue.” Snowden continued: “To be clear, ‘this president’ means this president, right now. Not the next one. There is still time to act.” Insurgent publisher WikiLeaks tweeted a reminder to those in the US who “let Obama legalize” assassinating anyone, spying on everyone and prosecuting publishers and sources alike. “It’s all Trump’s in 69 days,” they warned.
During his election campaign, Trump shot off a litany of verbal missiles that should have sunk his own candidacy. Echoing darker periods in US history, such as the FBI’s COINTELPRO which carried out covert, violent and illegal actions against domestic groups, Trump called for surveillance of mosques, suggested he might direct his attorney general to investigate the Black Lives Matter movement, and threatened journalists and freedom of the press. These threats by Trump, as worrisome as they are, are not new. After the September 11, 2001 terror attacks, New York City police systematically surveilled Muslims. The FBI surveilled the Black Lives Matter movement in Baltimore following the death of Freddie Gray in April last year. And during his eight-year term, Obama has persecuted more whistleblowers under the archaic 1917 Espionage Act than all previous presidents combined.
Trump has promised to bring back waterboarding interrogation methods and even apply “unthinkable” torture techniques. He has expressed his wish to fill the Guantánamo Bay prison camp in Cuba with more prisoners. He demanded that Apple help the FBI unlock the iPhone belonging to a San Bernardino shooter. He will oversee Obama’s drone program. Trump’s list of vile promises and possibilities spans from the dark and macabre to the dark and comedic. Even those of Dr Strange Love proportions instil a macabre sobriety about the situation. Ten former US nuclear launch officers have expressed concern about Trump gaining access to nuclear weapons. These officers, who were responsible for executing nuclear launch orders, signed a letter warning that Trump should not have his “finger on the button” because of his volatile temperament.
There are good reasons to be deeply concerned about what Trump will do with his newfound presidential authority. He has, after all, vowed to take revenge on his adversaries. Whether he means this threat or was playing up the hatred of his xenophobic electoral base to whip up votes is unknown. But what we do know is that Trump’s election brings us into dangerous and uncharted territory.
First they came for the hashtags…
Before the US presidential election, in April 2016, members of more than 90 Native American nations converged on Standing Rock in North Dakota to protect sacred tribal sites and their water supply. They gathered to protest the construction of the Dakota Access oil pipeline threatening to run through the grounds. By November, there had been reports of direct monitoring including ground and air surveillance. Protesters reported low-flying helicopters frequently hovering over camps, sometimes shining bright spotlights in the middle of the night. Activists were concerned about invasions of privacy including conversations being recorded even when they were uncertain of being monitored at any given moment.
The concern about constant surveillance at Standing Rock continued to threaten protesters in late October, when a Facebook post emerged that the Morton County sheriff’s department was using Facebook check-ins to target people at the protest camp. A campaign started on the social networking platform calling on people to “check in” at Standing Rock, and to share this request with their networks, to overwhelm and confuse police. Just over 24 hours after the call more than one million people had checked in to the Standing Rock reservation. Some are concerned that police could use the check-in data to track networks of people sympathetic with the groups protesting.
Recent research confirms that police use of social media surveillance software to glean personal information that we publish on our networks is escalating. In September 2016, the American Civil Liberties Union (ACLU) received thousands of public records revealing that law enforcement agencies across the state of California “are secretly acquiring social media spying software that can sweep activists into a web of digital surveillance.” The software monitored “threats to public safety” by tracking hashtags such as #BlackLivesMatter, #DontShoot, #PoliceBrutality and more.
The ACLU reports that, of 63 law enforcement agencies in the state, twenty have acquired powerful social networking surveillance tools such as MediaSonar, X1 Social Discovery and Geofeedia. Worse still, the ACLU notes that they found no evidence that these law enforcement agencies intend to give public notice, hold debate, gather community input or lawmaker votes about use of this invasive technology. No agency “produced a use policy that would limit how the tools were used and help protect civil rights and civil liberties.” It is seemingly and unfortunately common that police forces surveil communities without seeking public consent first. Perhaps they anticipate public objection.
Eyes Across the Skies
Standing outside the Circuit Court for Baltimore City in late June, two dozen people held signs demanding justice for Freddie Gray. Gray, a 25-year-old black man, died in police custody in April 2015. Inside the court, the prosecution argued that officer Caesar Goodson had driven his police van recklessly through the city deliberately tossing Gray’s body around in the back of the van. The reckless ride broke Gray’s neck.
Outside the court, a man standing with the protestors wondered why, with hundreds of street-level cameras around, Baltimore City police did not have video of the incident that led to Gray’s death. Not only were there many cameras that could have recorded something but the city’s police had been testing, without informing the public, an aerial surveillance system adapted from the US military surge in Iraq. An investigation by Bloomberg revealed that the surveillance system uses wide-angle cameras to capture about 30 square miles at any given moment, sending images in real-time to analysts on the ground. The footage is then stored and available for review, weeks later if necessary. The judge acquitted officer Goodson of all charges in the case of Gray. And yet the aerial surveillance system Baltimore police are testing hovered above those protesting outside.
While cameras were not reported to have captured the events that led to Gray’s death, the FBI has released their own video footage confirming surveillance of the Black Lives Matter movement. The FBI recordings date from April 29 to May 3, 2015, and were shot from piloted aircraft and drones. These and other reports, such as the FBI’s surveillance of earlier Black Lives Matter protests that erupted after the 2014 police shooting of 18-year-old black man Michael Brown in Ferguson Missouri, contradicts claims by FBI officials who say that the Bureau does not use spy planes to monitor peaceful protests.
In fact, an investigation by the North Star Post in 2015 revealed that at least 100 aircraft are being used by US law enforcement to spy on citizens. These aircraft are equipped with advanced, very high-resolution imaging and video technology — specifically StingRay, the secretive bulk cellular phone-tracking technology, and likely infrared or other night-vision hardware. The Associated Press reported that over just a 30-day period it had traced at least fifty aircraft back to the FBI and had identified more than one hundreds flights in eleven states. But the FBI kept this secretive operation hidden from the US public by registering the aircraft to shell companies that do not exist.
Like the Greek mythological monster, Argos Panoptes, the FBI has placed its eyes across the skies of the nation to mass surveil the public and spy on protesters.
Like the Greek mythological monster, Argos Panoptes, the FBI has placed its eyes across the skies of the nation to mass surveil the public and spy on protesters. Panoptes — from the Greek “Παν” (all) and “οπτικος” (seeing) — was all-seeing because he had a hundred eyes covering his body from head to toes. This monster was the inspiration for utilitarian philosopher Jeremy Bentham’s proposed correctional prison, the “Panopticon.” Using the model as a metaphor, French philosopher Michel Foucault argued that it illustrated defining power relations in everyday life. Authorities hope that if there is a spying camera overhead — via aircraft, drone, CCTV, any electronic device, or geolocation technology in your maps and social networks — that you will self-correct your behavior. Even if they are not actually spying on you, the threat of someone doing so will go a long way toward maintaining order.
The Economics of Surveillance Capitalism
In his 1964 book, One-Dimensional Man, philosopher Herbert Marcuse argued that in technologically advanced societies totalitarianism can be imposed without terror. This occurs through the transformation of private life into part of an overall system of domination. For Marcuse, the sphere of mass consumption, for instance, went beyond fulfilling basic needs to provide more comfort, luxury and affluence. These incentives not only mask the everyday oppressions that people experience, but they also act as a veneer that traps people’s imaginations from envisioning a different, possibly better way of living.
 In today’s technologically advanced information and communications driven world, the process of transforming private life into an overarching system of domination occurs surreptitiously — even if the final product appears everywhere.
In today’s technologically advanced information and communications driven world, the process of transforming private life into an overarching system of domination occurs surreptitiously — even if the final product appears everywhere.
Yahoo, for example, is aiming to patent “smart billboards” that will be placed next to freeways, in airports, on ferries, in bars and hotels, public transit systems, intersections and in other public and private spaces. These digital billboards will rely on a range of invasive surveillance technologies such as cell towers, mobile apps, images, video cameras, vehicle navigation, satellites, drones, microphones, motion detectors and “biometric sensors” such as fingerprint, retinal and facial recognition devices. Yahoo’s smart billboards will aim to identify specific individuals, and those who are in the same place at the same time, to determine their demographic data and socio-economic status. They will build profiles on people in their surroundings before serving personalized ads to them. Yahoo has termed this process “grouplization.” Others have labeled this exploitation of personal data for corporate gain as “Stasi capitalism.” New social theories are rapidly emerging in this area.
The process through which technology responds to individuals and groups to surveil and modify human behavior in scalable and profitable ways has been described by Shoshana Zuboff, Professor Emerita at Harvard Business School, as a new sub-species of capitalism known as “surveillance capitalism.” Zuboff describes surveillance capitalism as “a new logic of accumulation.” It is “a novel economic mutation bred from the clandestine coupling of the vast powers of the digital with the radical indifference and intrinsic narcissism of financial capitalism and its neoliberal vision that have dominated commerce for at least three decades, especially in the Anglo economies.”
The incredible evolution of computer processing power, complex algorithms and leaps in data storage capabilities combine to make surveillance capitalism possible. It is the process of accumulation by dispossession of the data that people produce. It occurs in both profound and seemingly benign ways.
Beyond Virtual Reality to Real Liberation
Technologically advanced societies produce ever more personalized lifeworlds. Responsive algorithms suggest the next Netflix video series we can binge watch. Amazon Prime recommends products we might like delivered the next day. Augmented Reality and Virtual Reality games, which supplement and provide revolutionary digital possibilities, are on the rise. This drive towards personalization combines with the latest developments in technology to provide a sense of choice and life satisfaction in a world full of overwhelming inequality and injustice.
The appearance of affluence, the sensation that all knowledge and virtual possibilities are available on the web, at our fingertips, in the palm of our hand, surrounding us wherever we go, is a pixilated distraction from the structural oppression embedded in the totality of everyday life. It is an intoxicating distraction from those who struggle to protect their communities, such as the indigenous peoples at the Standing Rock occupation and the Black Lives Matter movement. It is a distraction from sexism, disempowerment, environmental decay, class rule and racism, while in many ways it also galvanizes these same problems.
What is required today is radical imagination to re-envision how powerful technological change could be repurposed to feed and house the poor, to provide health, education and culture to everyone, to decentralize societies and achieve self-governance, classlessness and democratic autonomy. The number of active virtual reality users is forecast to grow to 171 million by 2018. For people who imagine whole new worlds all the time, imagining just one new world — our own — in which there are ecologically friendly smart homes, smart cities, smart schools and smart hospitals for everyone should not be too difficult. The technology exists. Achieving “communal luxury” for everyone is now more possible than ever.
Yet large firms and state institutions have appropriated and transformed information and communications technologies into some of the most powerful tools for social control the world has ever known. Their networks, platforms and surveillance apparatuses have enabled a dangerous fusion of public and private power and are clearly designed to cement their own positions of privilege and domination. It is up to us, the people and communities most affected, to fight for the re-appropriation, decentralization and re-creation of these technologies in order to make possible new and better ways of living.
Source URL — https://roarmag.org/magazine/mass-surveillance-smart-totalitarianism/
Next Magazine article
Algorithmic Control and the Revolution of Desire
- Alfie Bown
- December 18, 2016
The Dog-Whistle Racism of the Neoliberal State
- Adam Elliot-Cooper
- December 18, 2016

